Blog
The dogesec blog
-
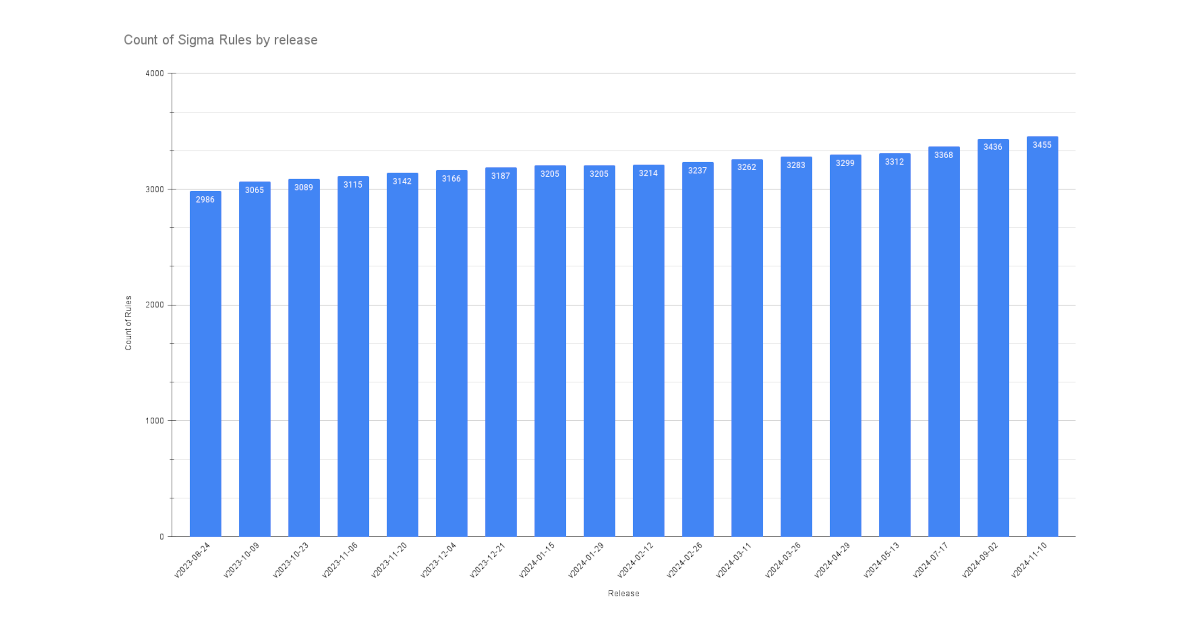
An Analysis of the Latest Sigma Rules Release
RESEARCH December 09, 2024
In this post I walk you through the database queries we use to compare Sigma Rules releases. We use these to identify the detail of what has changed before we push any updates internally. -
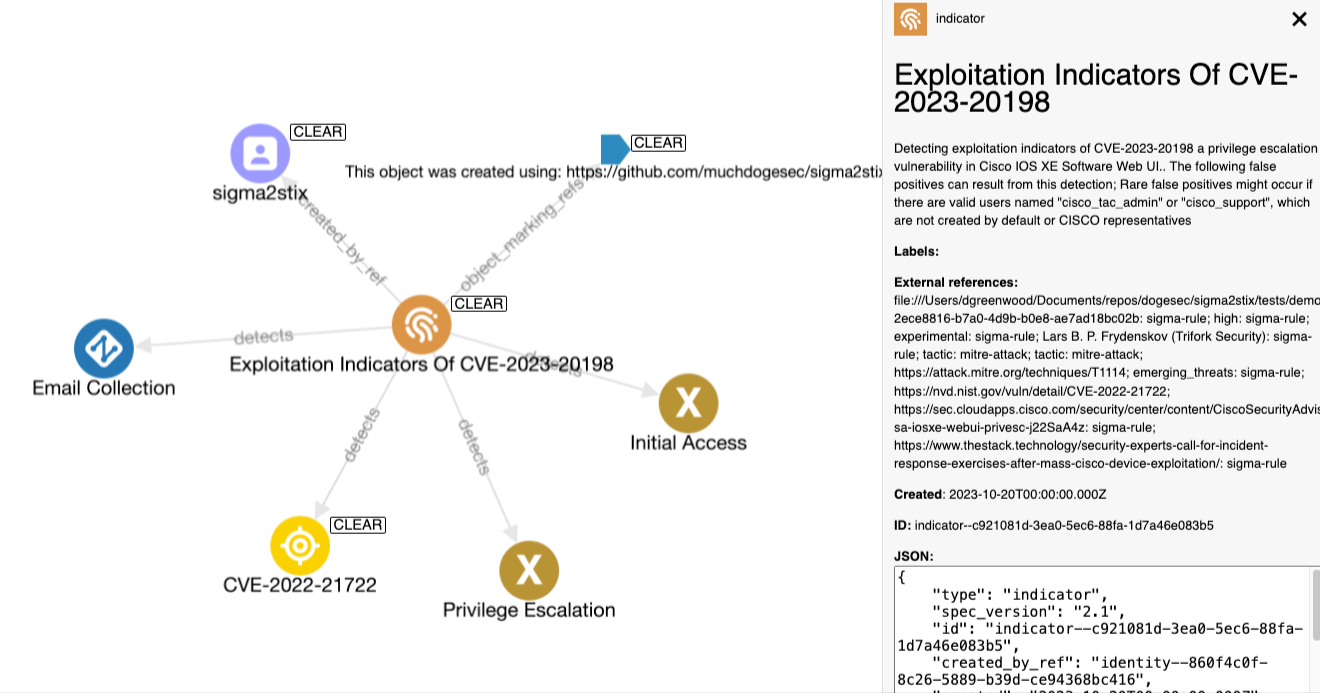
Importing Sigma Rules into a Threat Intelligence Platform
RESEARCH December 02, 2024
We needed a way to link all of our threat intel research to detection rulesets in one place. Our solution; model Sigma Rules as STIX objects. -
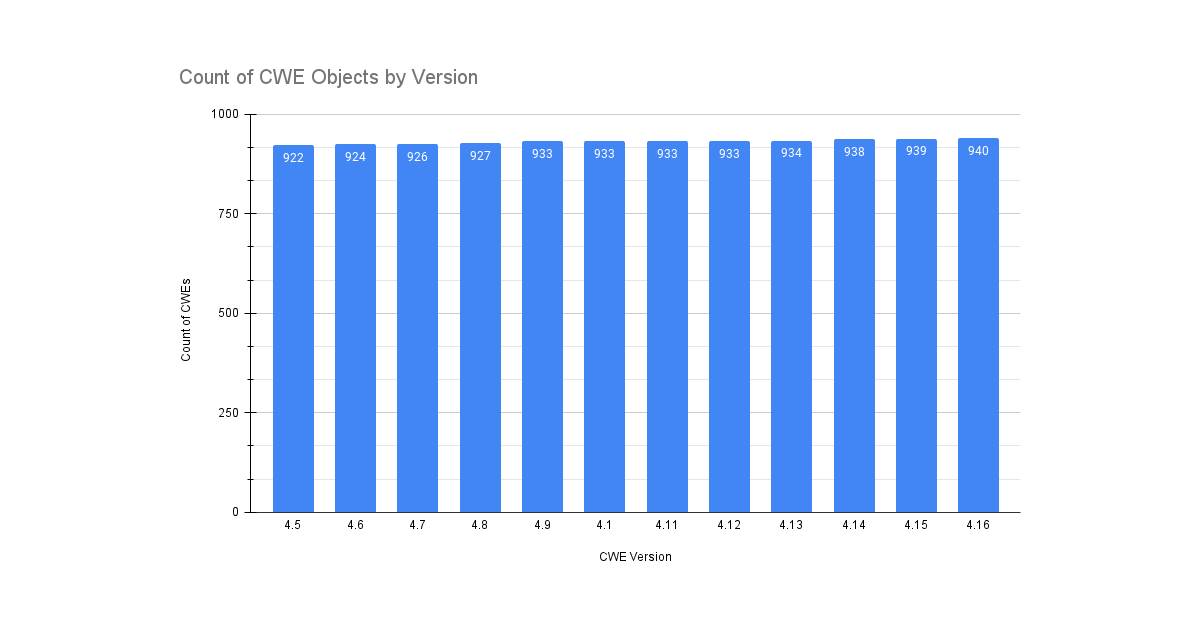
An Analysis of the Latest CWE Release
RESEARCH November 25, 2024
Last week saw the release of CWE v4.16. I took a deeper look into the latest release so you don't have to. -
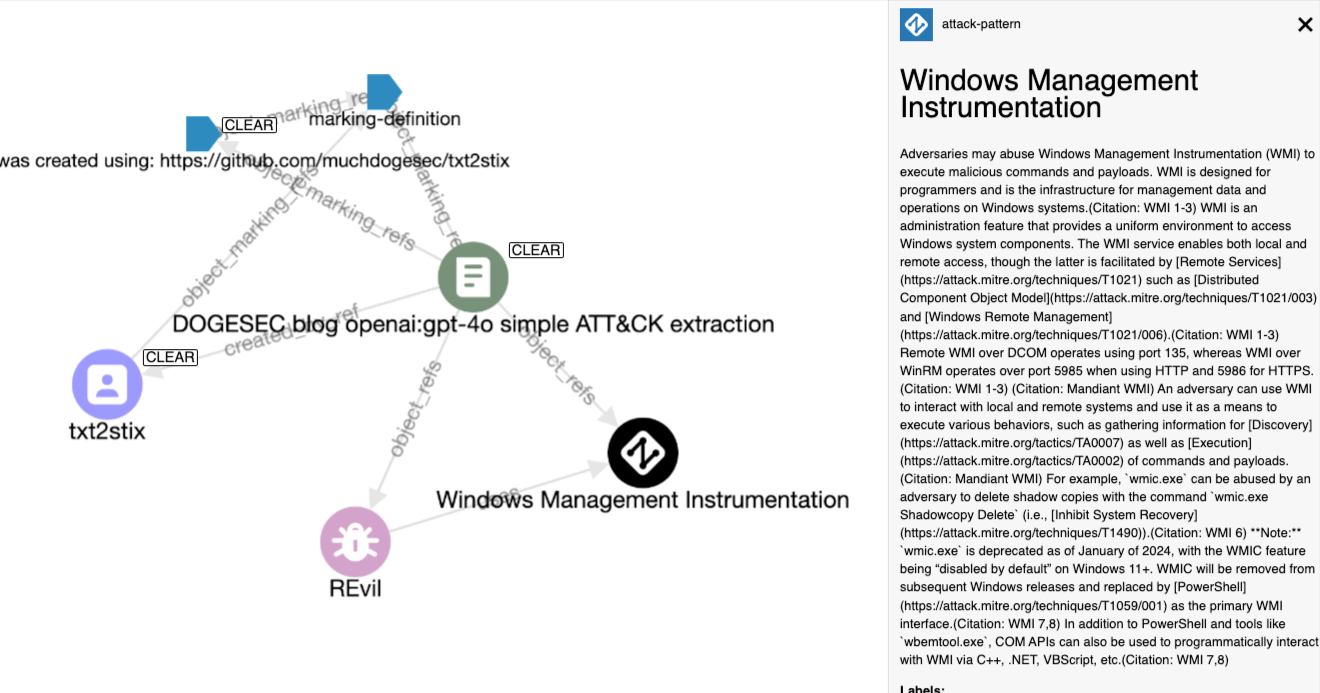
How do Public AI Models Perform at Extracting TTPs from Intelligence Reports?
PRODUCTS November 18, 2024
I pitch OpenAI, Anthropic and Google against each other to see which one best understands MITRE ATT&CK -
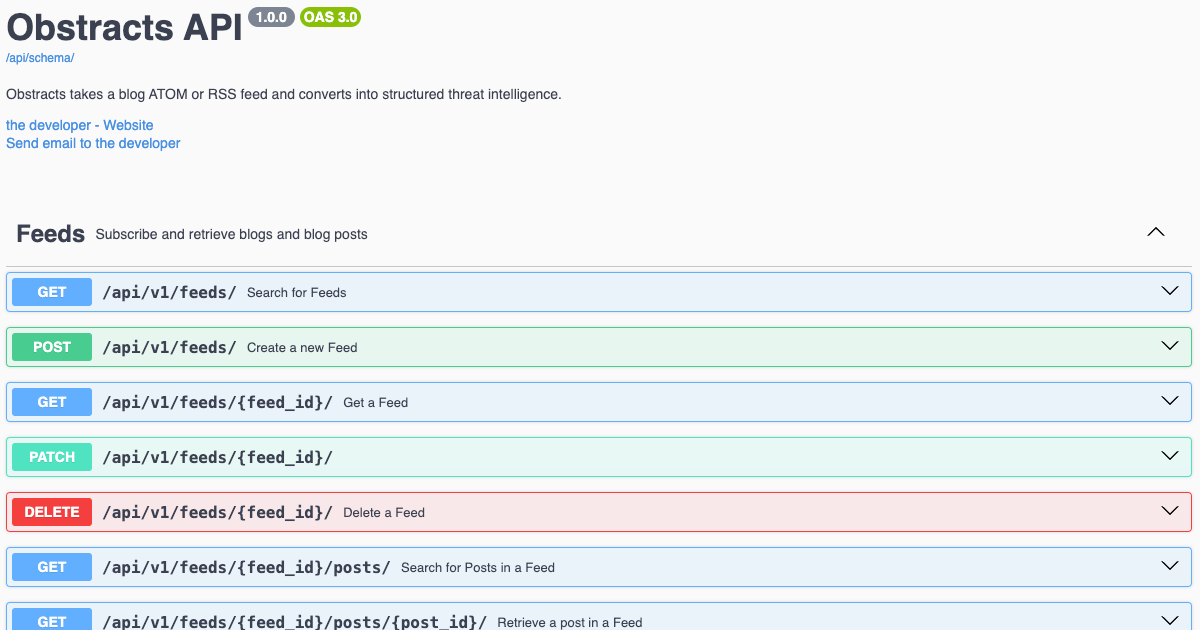
Turn any Blog Post into Structured Threat Intelligence
PRODUCTS November 11, 2024
Obstracts is the blog feed reader used by the worlds most targetted cyber-security teams. Let me show you why. -
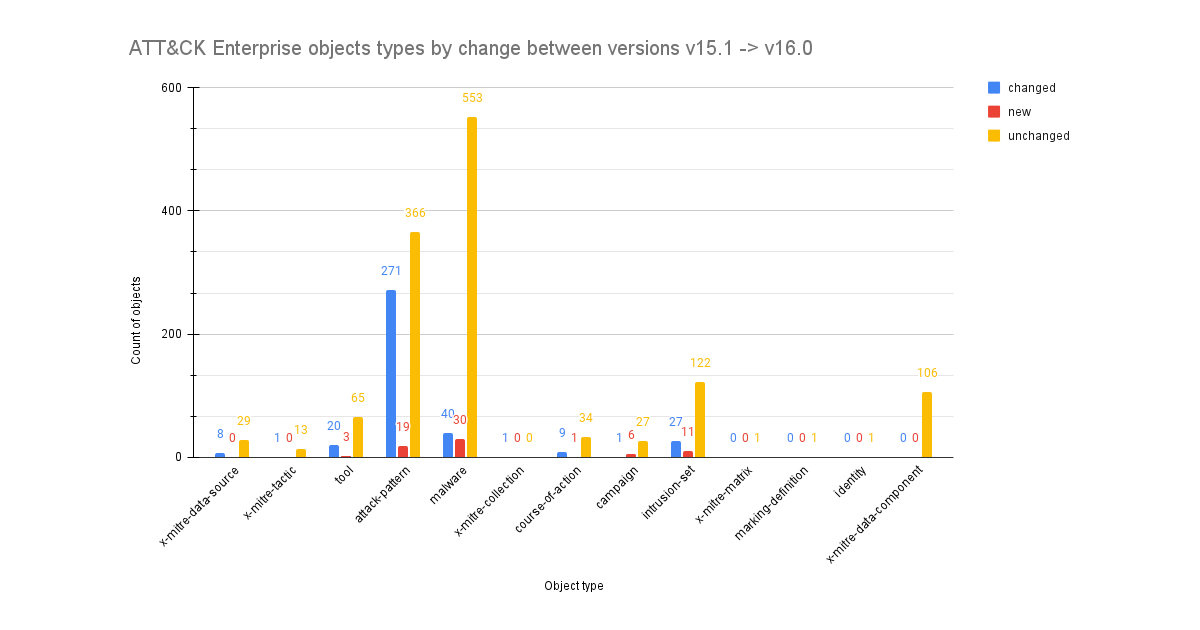
An Analysis of the Changes in ATT&CK Version 16.0
RESEARCH November 04, 2024
Your handy guide to streamlining upgrades of MITRE ATT&CK by comparing the changes made between releases. -
Bad Software Keeps Cyber Security Companies in Business
RESEARCH October 28, 2024
Despite countless frameworks, best practices, blog posts... so many developers still hardcode credentials into their code. -
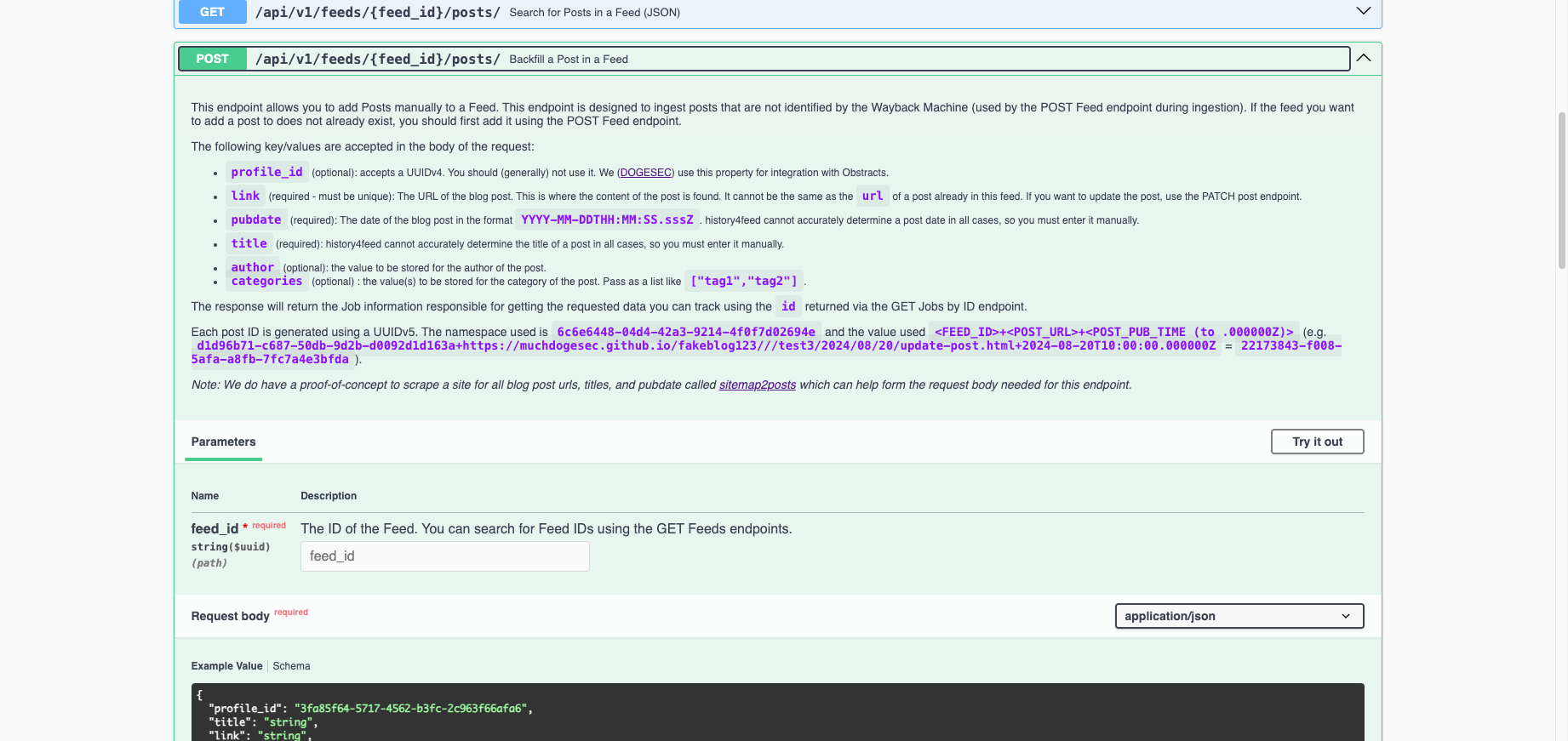
When the Wayback Machine Went Down, so did our Software
PRODUCTS October 14, 2024
A short lesson in why building a product with a single point of failure is bad (duh!), and our hunt for a Wayback Machine alternative. -
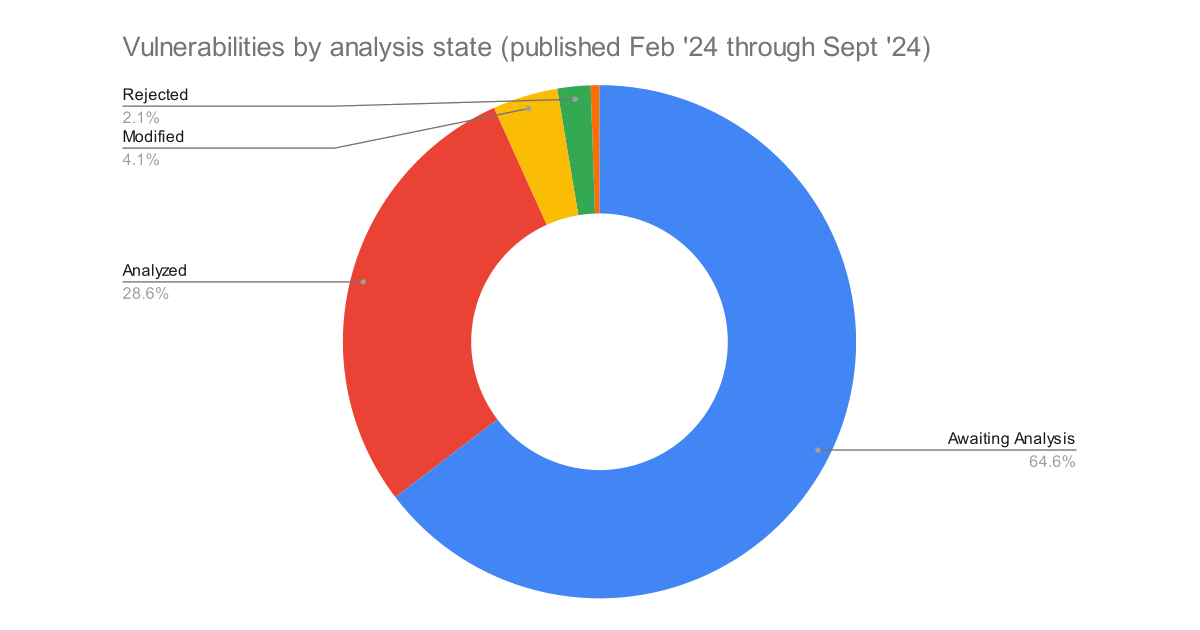
17,375 CVEs in the NVD Backlog, and Counting
RESEARCH October 07, 2024
The NVD are still struggling to keep up with the backlog of CVEs to be analysed. With 26,876 added since February, it is no surprise. -
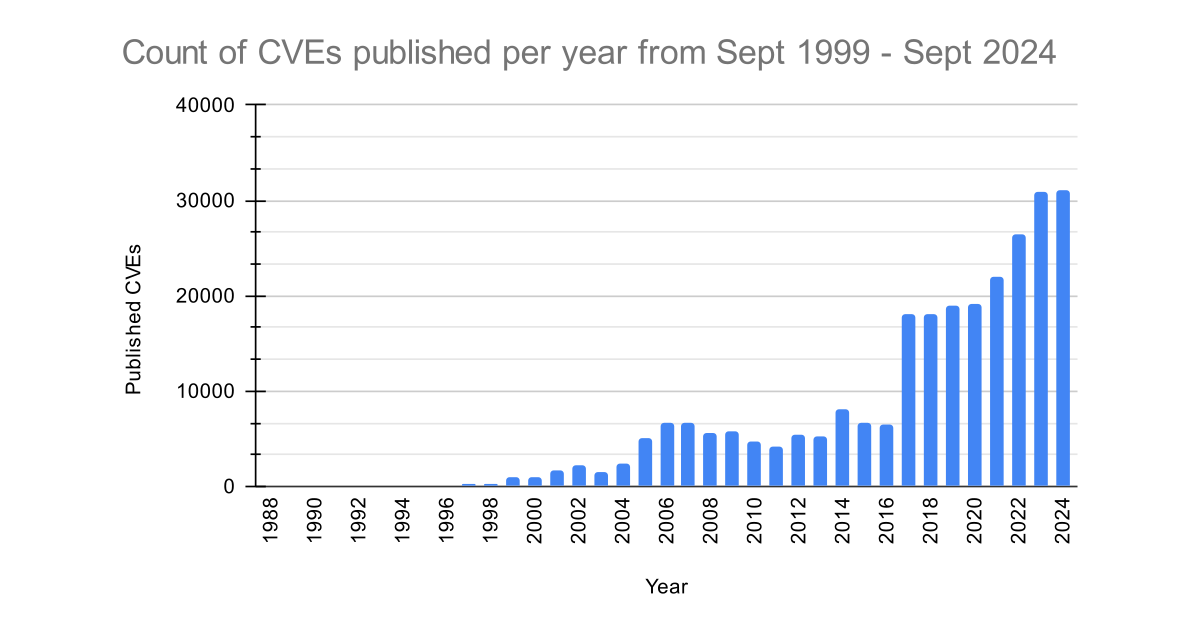
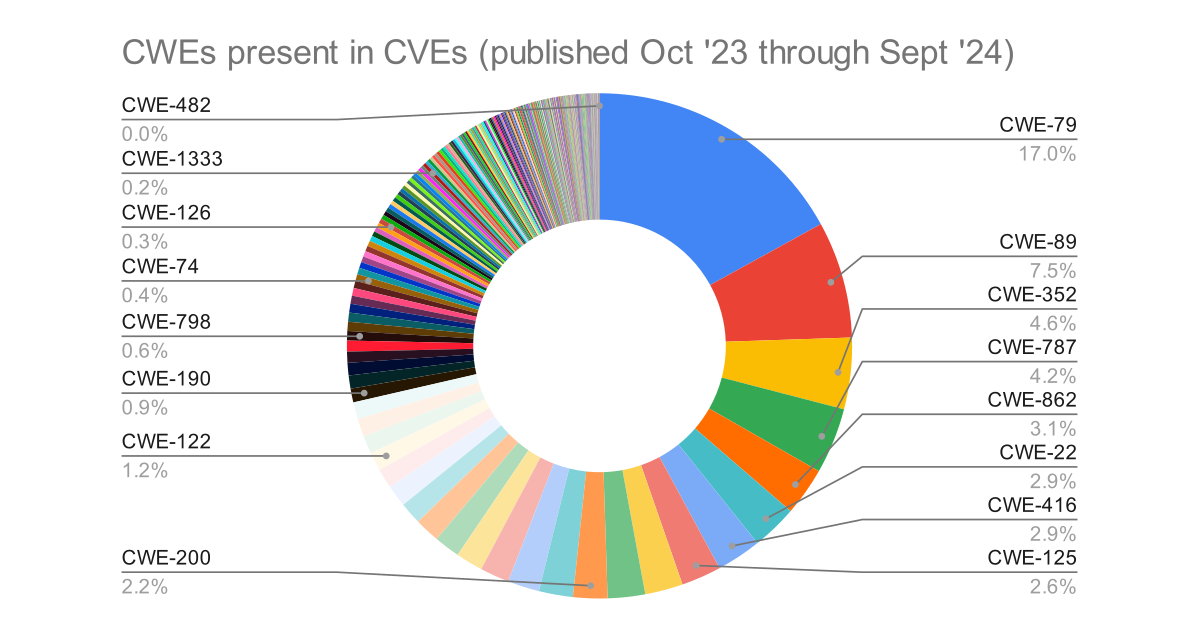
Analysing 25 Years of CVEs
RESEARCH September 30, 2024
The CVE List was launched in September 1999, listing 321 CVE records. 25 years later there are 265,767 CVE records.